AI systems are moving fast into our real environments, often without clear visibility. AI Exposure Security focuses on identifying, monitoring, and reducing these risks.


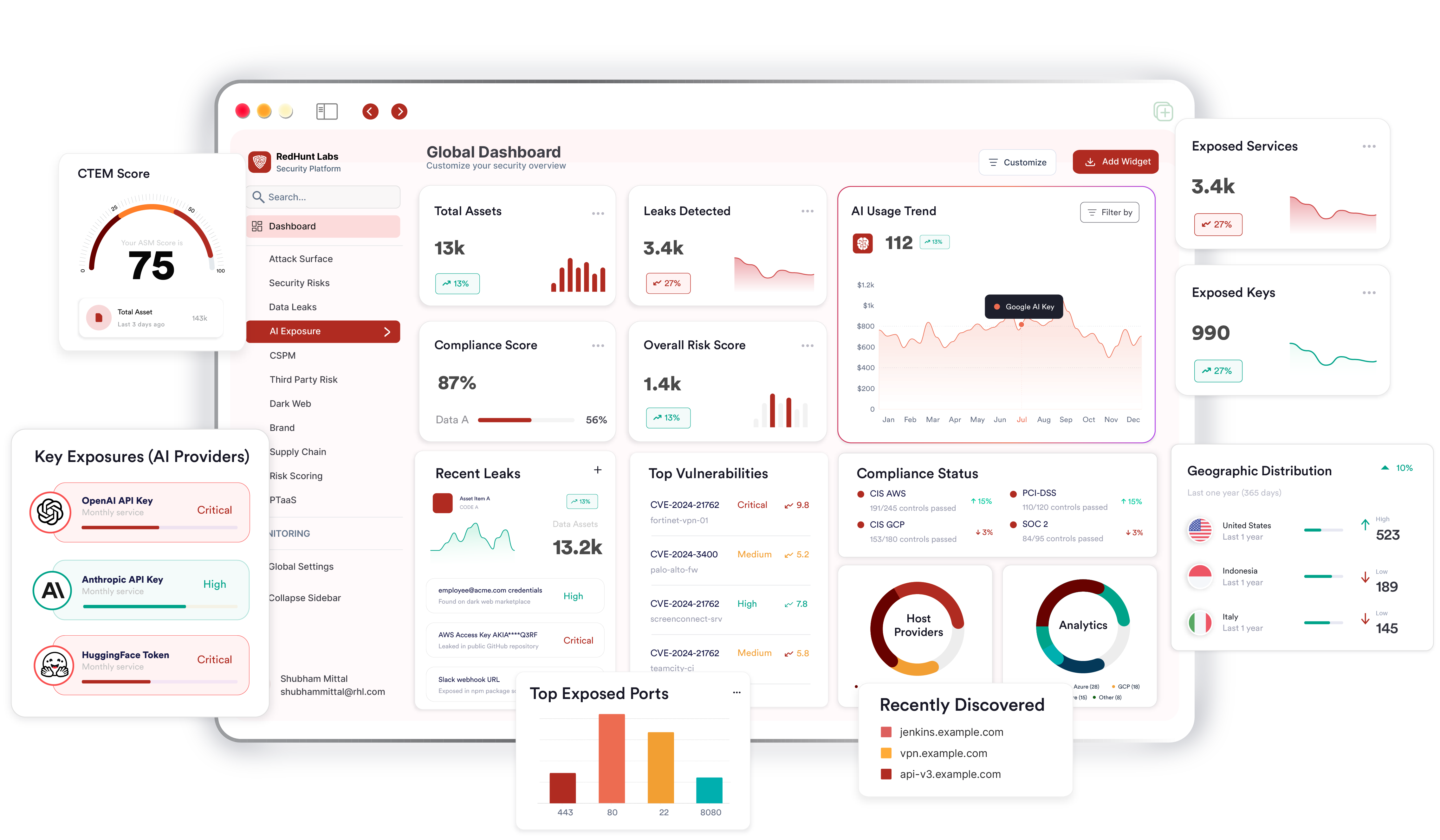










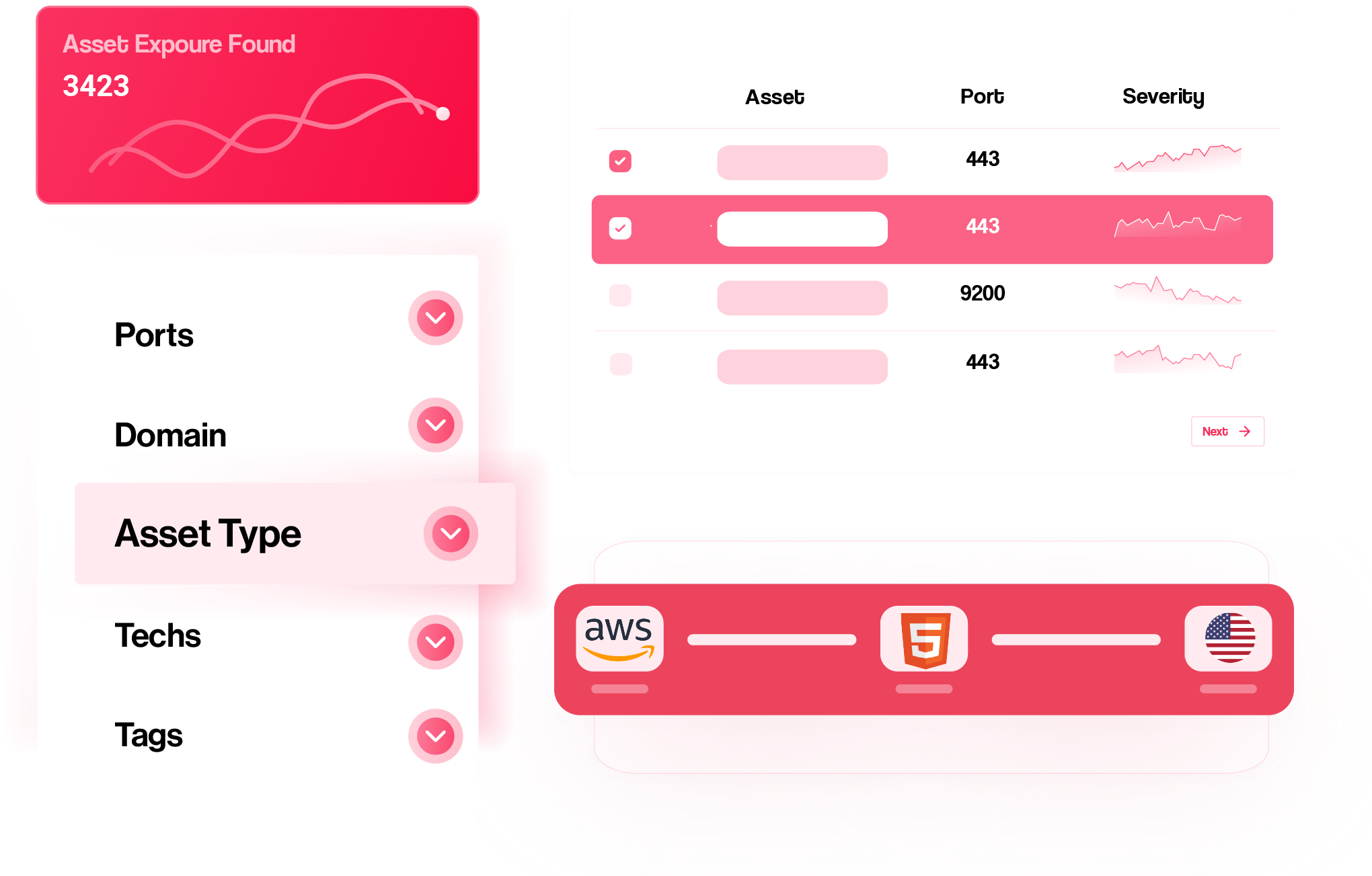
Stay ahead with our cutting-edge asset discovery that identifies and maps your digital landscape in real-time, ensuring no element is left unaccounted for.
AI systems are moving fast into our real environments, often without clear visibility. AI Exposure Security focuses on identifying, monitoring, and reducing these risks.
Safeguard sensitive information. Our data leak discovery feature identifies potential leaks, enabling you to take immediate action to secure your data.
Proactively manage risks with our security risk discovery and Vulnerability Assessments. Identify vulnerabilities and threats, get real-time insights and stay ahead in cybersecurity landscape.
Extend your security perimeter. Discover and assess third-party assets that may impact your data, ensuring a holistic approach to your organization’s digital risk landscape.
Ensure airtight cloud security.
Our platform conducts a thorough review of your cloud infrastructure, identifying and addressing security gaps for comprehensive protection.
Gain continuous visibility of your ever-evolving Attack Surface, whether originating from your dynamic infrastructure, cloud components, sales & marketing teams, mergers/acquisitions, or scattered third-party integrations.

Gain continuous visibility of your ever-evolving Attack Surface, whether originating from your AI environment, dynamic infrastructure, cloud components, sales & marketing teams, mergers/acquisitions, or scattered third-party integrations.












"Continuous and immediate alerting of vulnerabilities cutting away from the noise helped us in identifying and remediating the vulnerabilities proactively. We were able to timely identify the security gaps and improve our security posture."