Introducing Free Attack Surface Recon API by RedHunt Labs
Introduction
In the ever-evolving landscape of cybersecurity, staying ahead of potential threats is paramount. As the digital realm expands, so does the attack surface of organizations, presenting a challenge for information security professionals, bug hunters, security researchers, ASM vendors, penetration testers, and MSSP vendors alike. To address this need for enhanced domain reconnaissance and asset gathering, RedHunt Labs proudly presents the powerful and versatile Recon API.
The Recon API developed by RedHunt Labs is a game-changer in the world of information security. Its primary objective is to empower cybersecurity enthusiasts, professionals, and organizations with the ability to bolster their reconnaissance capabilities significantly. Whether you are a seasoned bug hunter or a curious security researcher, this API is designed to elevate your recon game to new heights.
At the core of the Recon API lies a vast and meticulously curated database of attack surface intelligence. With over 6.7 billion records, the API offers a comprehensive repository of invaluable information. This intelligence includes but is not limited to:
- 3+ Billion Subdomains & Domains: Discover hidden assets and lesser-known entry points that might otherwise be overlooked during traditional reconnaissance.
- 1.9+ Billion Commits & Correlations: Unearth potentially leaked credentials and data breaches associated with the target organization, helping you assess their security posture more effectively.
- 2+ Billion Third-Party Assets Correlations: Identity connections and associations between various third-party assets and the target organization, allowing you to map potential vectors for exploitation.
The Recon API serves as a force multiplier, enabling security professionals and bug bounty hunters to expand their scope and gain valuable insights into an organization’s attack surface. By leveraging the wealth of information provided by the API, you can proactively identify and address security vulnerabilities, safeguarding your own systems and those of your clients.
Who can benefit from this Attack Surface Recon API?
- BugBounty Hunters
- Penetration Testers
- Attack Surface Management Vendors
- Threat Intelligence Teams
- MSSP Teams
- Security Researchers
How to Use/Consume the API
In this section, we will provide a practical demonstration of the Attack Surface Recon API by RedHunt Labs. By showcasing the API’s powerful capabilities and real-world applications, we aim to illustrate how it can be effectively utilized to enhance cybersecurity efforts. Through various scenarios and use cases, we will delve into how bug bounty hunters, security researchers, penetration testers, managed security service providers (MSSPs), threat intelligence teams etc. can leverage the API to bolster their reconnaissance game.
Head over to our developer portal and create a new account by clicking on the Login button and then clicking on “Create an Account”.
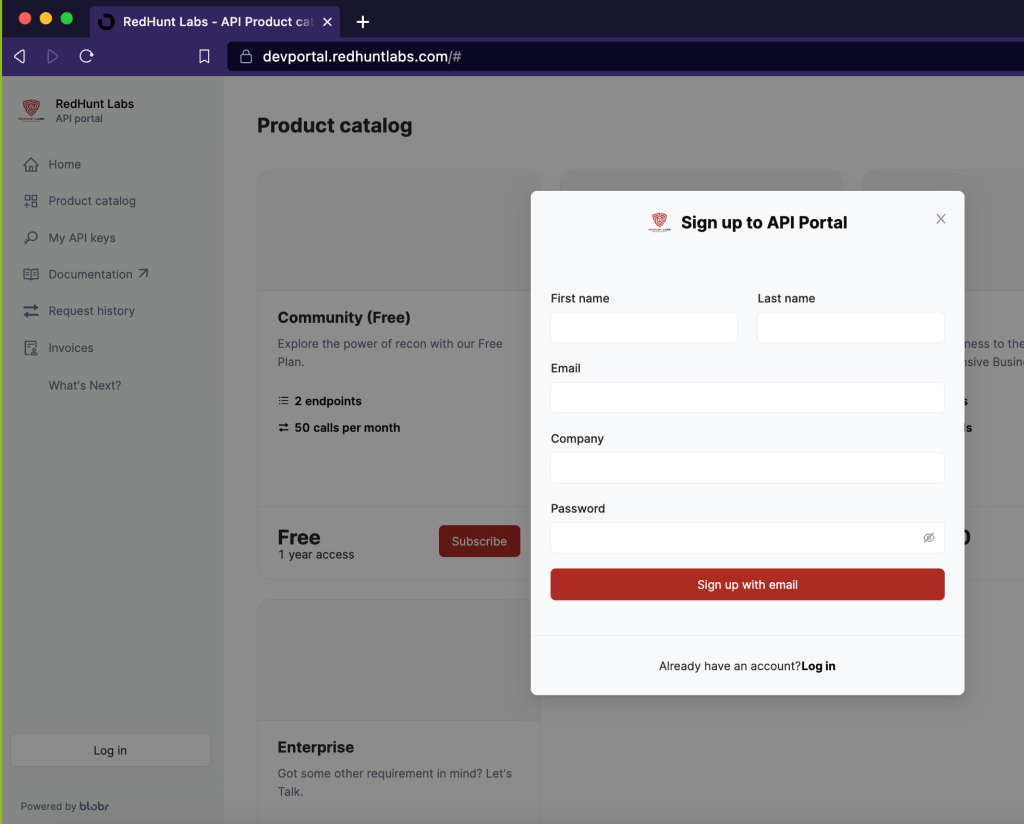
Head over to the Product Catalog section and choose the plan that suits you best.

Navigate to the My API Keys section and fetch your access keys for making requests to the Attack Surface Recon API.

In the product catalogue section, click on the plan’s box that you have subscribed to and it should open a new page showing all the available endpoints, like below.
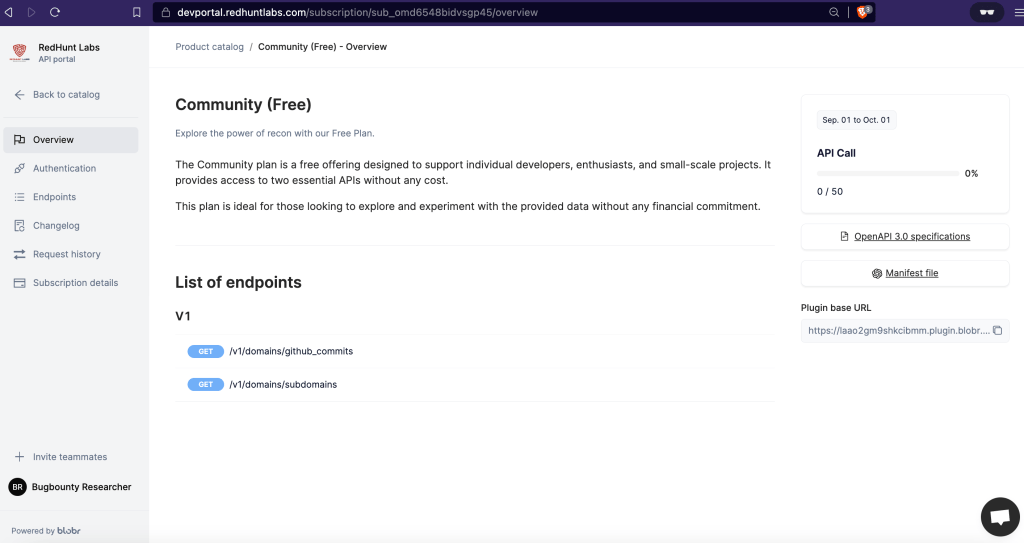
We also offer a free plan that gives you 50 API calls per month giving you an insight on how our API works and how well it can cater to your needs.
For this demonstration, we will click on the /subdomains endpoint to see how we can use the Attack Surface Recon API to gather subdomains for a given target. The endpoint accepts three values, a domain (required) which you would like to gather the subdomains for, a page_size (optional) value that helps the user limit how many assets to display per request with the default page_size being 100, and finally page (optional) value that will let the user iterate over all the results of a subdomain divided into pages.
Let us now try to make a request to this endpoint through 3 common ways and see how it works,
1. Using the Dev Portal
Add a domain within the domain input and click on the red button which says “Try it out”. The page will process the domain and return the response as we can see in the below screenshot,

The request body section shows the structure of the JSON response that will be returned when a request is made to that specific endpoint. In the response tab, you will notice all the subdomains that the Attack Surface Recon API returned.
2. Using Curl Request
If you scroll down, you will notice that the page also contains a code snippets section displaying the sample code snippets for making a request to the Attack Surface Recon API with your input and the API key.
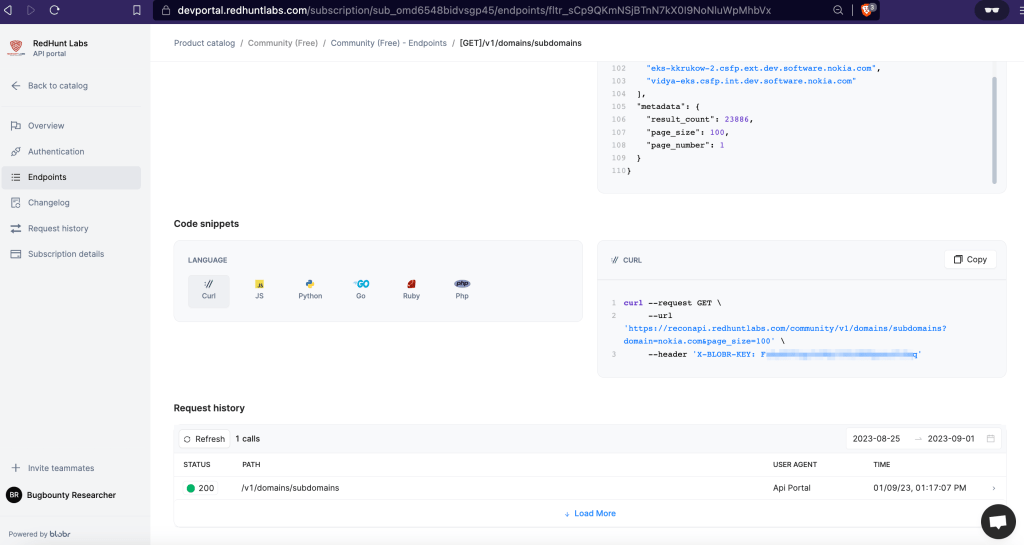
As you can see in the above image, by default we get to see a curl request snippet generated by the portal. Let us replace it with our API key and see it in action.

Once the request is made you will get the JSON response similar to the response body that we discussed earlier, as you can see in the above screenshot.
3. Using Postman Collection
Using the Attack Surface Recon API through Postman is pretty straightforward. Documentation for the PostMan Collection is hosted at https://documenter.getpostman.com/view/17809599/2s946pYoma
Simply to your Postman API client and open a new Request tab. Fill the URL field with the desired API endpoint and the additional parameters as well as click on the Headers tab and add the API key as we can see in the below image. (Or simply use the collection and run it in Postman).

Make sure to replace google.com with your own target and replace the REDACTED string with your unique API key. After adding all the necessary input and clicking on the Send button, you will find the subdomain results within the response body if everything was passed correctly.

In the above image, we can see the response the API returned when we passed google.com as a target with our unique API key which has been redacted for this example.
In case you’d like to know more about the working of the API and the various endpoints it has to offer, be sure to check out the Documentation for more details!
Conclusion
At RedHunt Labs, our dedication to innovation knows no bounds. We are committed to continuously enhancing the Attack Surface Recon API to empower our users with cutting-edge tools and capabilities. As we speak, our team of experts is actively working on adding more features and endpoints to the API, ensuring that it remains at the forefront of cyber reconnaissance technology.
What’s Next?
Stay tuned for exciting updates and expansions to the API’s data coverage, usability, and analytical capabilities. As the community enjoys the API, we will keep adding more interesting endpoints.
With your valuable feedback and support, we are driven to shape the future of cyber reconnaissance, making it more powerful, efficient, and accessible to all. Together, we will forge a path towards a more secure digital landscape.
Sign Up for the API Here: https://devportal.redhuntlabs.com/home


[…] Detailed instructions can be found here: https://redhuntlabs.com/blog/introducing-a-free-attack-surface-recon-api-by-redhunt-labs/ […]
[…] Detailed instructions can be found here: https://redhuntlabs.com/blog/introducing-a-free-attack-surface-recon-api-by-redhunt-labs/ […]